Zero Trust Framework
Compliant Access
Delivery
Delivering and enforcing effective compliant access requires a flexible and intelligent IAM system that connects technology to business — via process mapping — enhancing your existing business model without costly customizations.
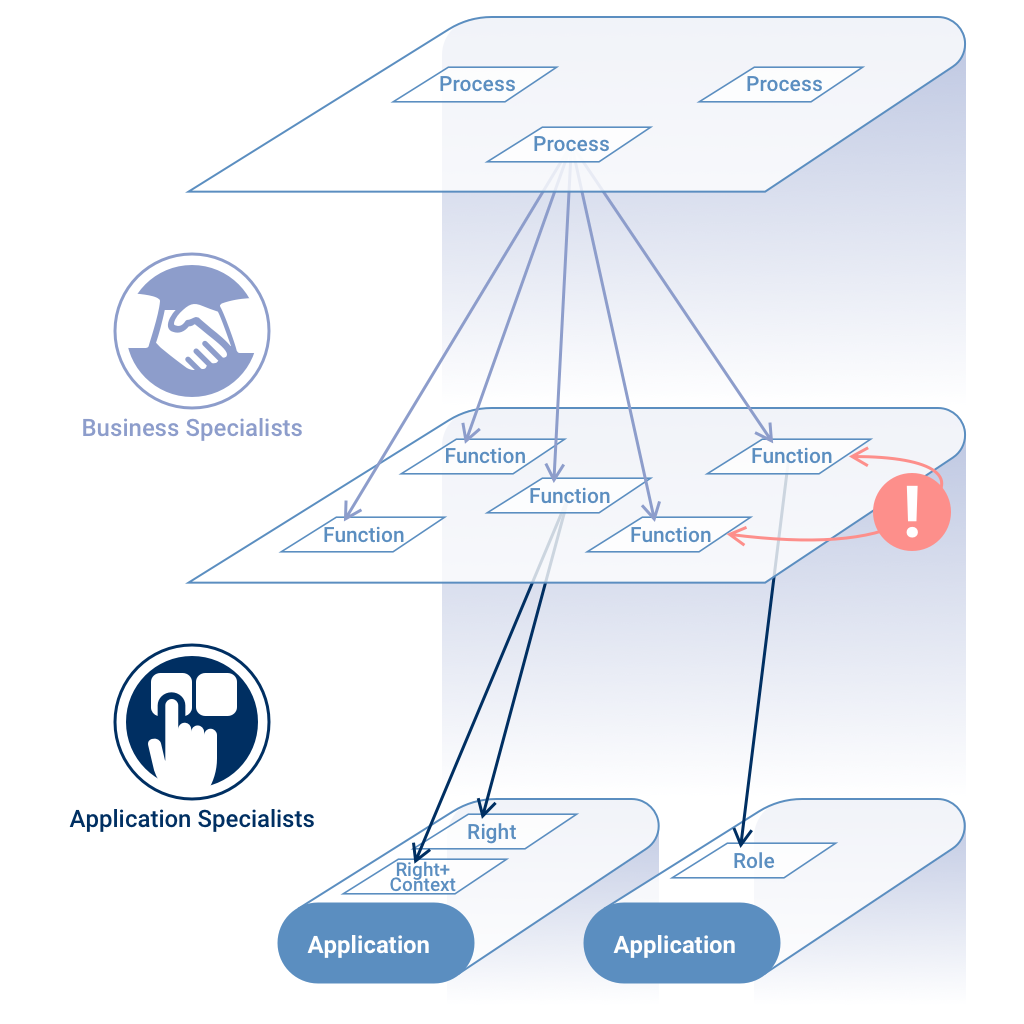
Clean Separation Between Business and Technical
The Foundation
What is "Compliant Access"?
Compliant access relates to minimizing the risk associated with granting access to business assets via standards and policies. Such access applies not only to people but also to systems, applications, programs, or other business-related resources.
Compliant Access Delivery uses a business modeling approach and synthesizes multiple Identity and Access Management (IAM) technologies to automate and maintain each user with the appropriate access to IT systems while continuously minimizing risk.
The difficulty is in the detail — and that is where traditional solutions miss the mark. The keys to Compliant Access are the words "appropriate" and "business policy":
- Appropriate — in relation to the access to be granted
- Business Policy — in relation to the tasks to be performed
An IAM system cannot deliver Compliant Access in isolation. Because each organization has their own particular language, processes, and policies, any IAM system must bridge the divide between the technical "system" world and the business "process" world.
It's important to note that an IAM system is nothing more than a tool to support the business and its policies. One of the fundamental issues organizations have with such systems is when inflexible software tries to dictate how you do business.
Within the business, existing operating processes, industry norms, and regulatory restrictions define what is job appropriate, what is a risk, and what is non-compliant. The software is there to fulfill and make that easy.
To achieve such goals, EmpowerID leverages an organization's business model and language to both enforce and provision Compliant Access across Cloud and on-premise systems.
Business Modeling
Business Processes and Functions
All businesses can be broken down into a series of business processes. Each process is a series of tasks that can be performed by internal or external participants.
Each individual task can be broken down into the functions that are executed in the process of completing that task. An example of a function would be the act of creating a purchase order within a larger purchasing business process.
Because such terminology is commonplace, business users can readily recognize the function of creating a purchase order. Managers and auditors can easily identify who within an organization should be entitled to create purchase orders.
Later, when managers need to review employee access rights periodically, it would be simple to see whether the ability to create purchase orders has been assigned to someone for whom it was no longer job appropriate.
Functions are the missing link that connects traditional technical access management with the world of business-friendly terms and recognizable job-appropriate access.
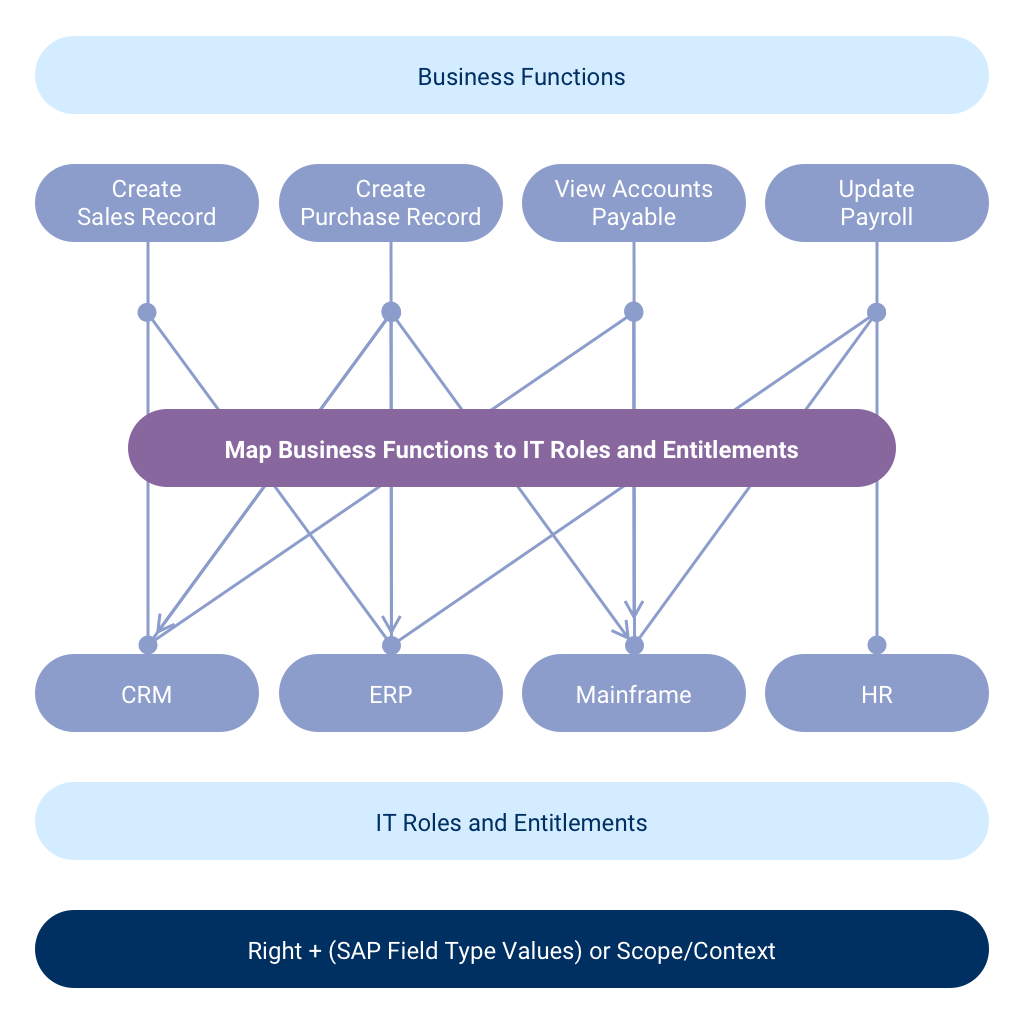
Mapping Business Functions to IT Roles and Entitlements
Policy Enforcement
Risk Policies
Compliant Access must be "appropriate" and adhere to an organization's "business policies." These policies are specific to each organization, tailored to match how they operate, their industry, processes, and regulatory requirements.
Business processes are non-technical in nature and are independent of the IT systems an organization uses. For example, an organization's Customer Acquisition Process and related risks do not vary based on whether they use Salesforce, HubSpot, or Excel as their CRM.
As part of this process, an organization can define what high-risk functions merit special attention. This could be an isolated function, or when combined with other functions and involving other factors like certain job roles.
Separation of Duties (SoD) Example
User A: Create Purchase Order
Low risk when isolated
User B: Approve Purchase Order
Low risk when isolated
Single User: Both Functions
HIGH RISK — SoD Violation
Security Framework
Zero Trust and Compliant Access Delivery
Organizational security is no longer a simple internal/external = trust/no trust equation. Zero Trust is the new framework for Compliant Access Delivery.
Never Trust
Access to systems must always be strongly authenticated
Always Verify
Authorization based on identity and request context
Least Privilege
Only absolute minimum access is ever given
The Last Mile Problem Solved
How is Compliant Access Delivered?
EmpowerID supports all modes of Compliant Access Delivery to maximize business value.
Gateway Enforcement
End users connect through a gateway that authenticates, authorizes, and monitors access. For web apps and APIs, this is known as Web Access Management (WAM).
Learn About Application GatewayClaims-Based Enforcement
Federated applications trust EmpowerID to deliver identity information and Compliant Access as claims during login. AWS IAM roles are a sophisticated example.
Learn About AuthorizationProvisioning Engine
EmpowerID provisions permissions or application roles using connectors. Essential for SAP ABAP systems with complex roles and profiles that can't use gateway or claims approaches.
Learn About ProvisioningSummary
Compliant Access is a critical component of every organization today. When selecting an IAM solution to deliver compliant access, remember that it cannot deliver compliant access on its own. It's only a tool to enforce your policies. Your own processes and policies are always the prime movers.
Deliver Compliant Access Today
See how EmpowerID bridges the gap between your business processes and IT systems.