Featured Case Study
World's Largest Azure AD Implementation
EmpowerID helps SIEMENS achieve Zero Trust AND Secure the World's Largest Azure Active Directory
Siemens was able to improve security through Zero Trust as well as increase productivity and reduce costs by automating and providing many tasks as self-service options.
The Challenge:
"Security is our main driver"

Deep Dive
Authorization Explained
A Guide to Authorization — 60 Pages
Download the whitepaper for a full 60 pages read
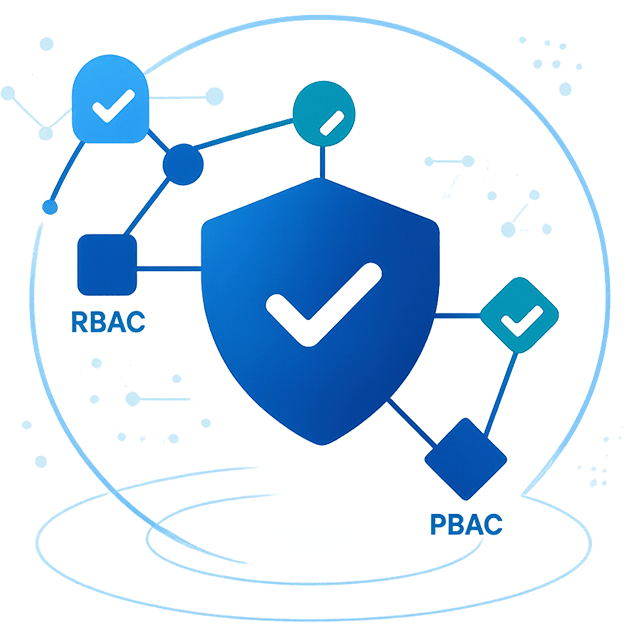
This new white paper provides an in-depth overview (60 pages) on authorization and how applications make decisions. Approaches for externalizing authorization using RBAC, ABAC, and PBAC are discussed and illustrated, highlighting their strengths, weaknesses, and where each performs best.
Download White Paper10 Pitfalls to Avoid
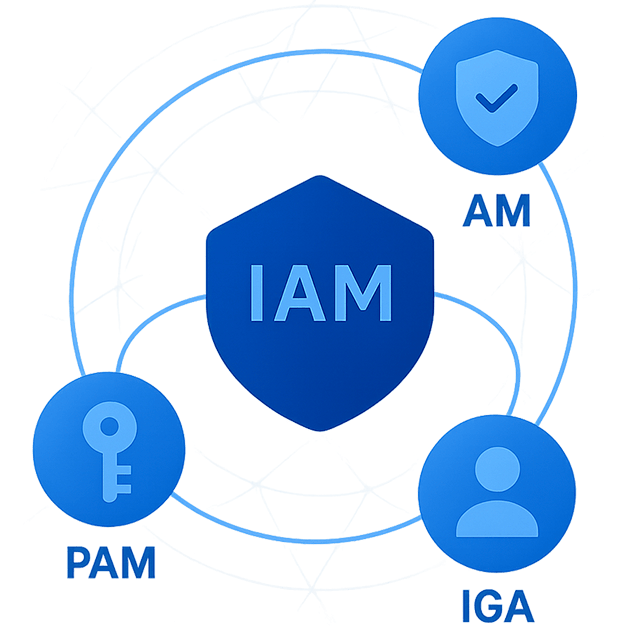
If your organization is contemplating an IAM solution then there are certain pitfalls that you need to be conscious of. Being aware of, and avoiding, these will aid you in making a good choice, not least in understanding, planning, and in timesaving.
Make Your Identity and Access Management Project a Success:
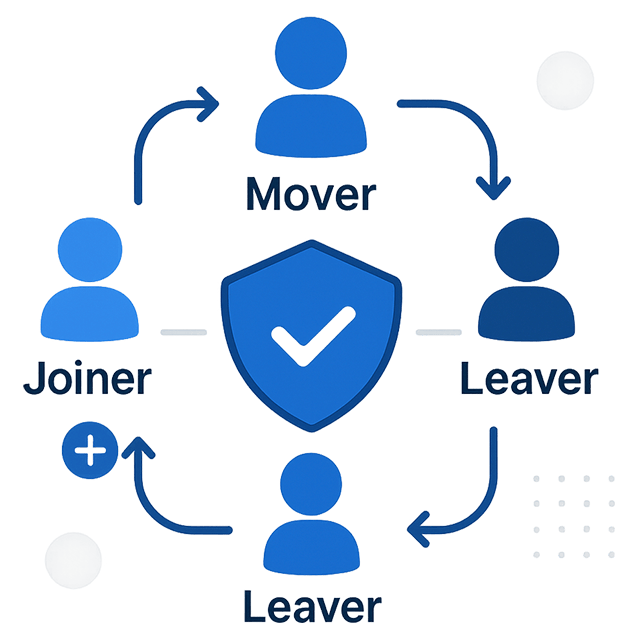
- Automate employee and contractor onboarding and termination
- Leverage role and attribute-based access control
- Provide self-service identity, group and password management
- Provide single sign-on to on-premise and cloud apps
- Manage privileged identities and access
- Save your help desk time and money!
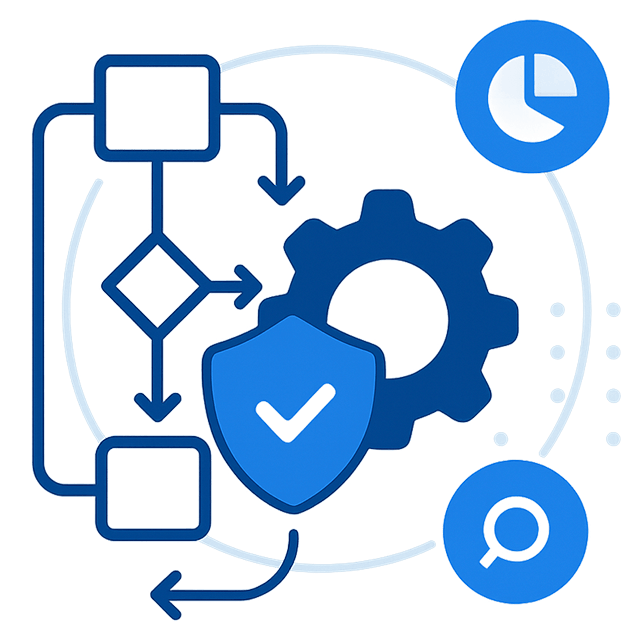
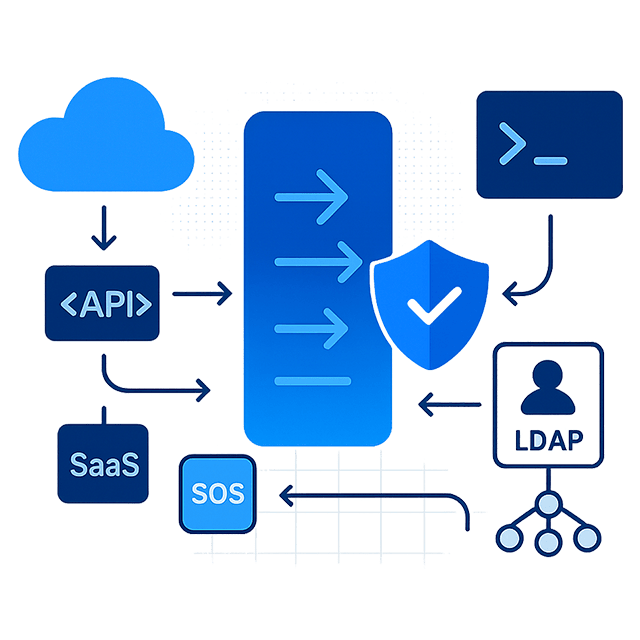
Azure RBAC Management
The elastic nature of the Azure infrastructure and the ability to allow rapid changes such as self-provisioning and deprovisioning of new services and IT resources make it difficult for security and audit teams to meet their regulatory obligations concerning asset management.
Find out how our Azure RBAC Manager empowers organizations to maintain an accurate understanding of their Azure security landscape, to optimize its management, and to ensure compliance with an organization's risk policies. Offering auditing, Zero Trust delegated administration, policy-based access assignment, self-service shopping, and access recertification for Azure security.
Download White PaperAnatomy of a Cyberattack
Learn about the identity perimeter and how attackers exploit vulnerabilities in identity and access management systems. This white paper provides insights into common attack vectors and how to protect your organization.
View reports and downloads
New Release
Extend Your Entra Investment
Elevating Entra with EmpowerID
Entra serves as the backbone of identity management for many organizations, but faces challenges in complex, hybrid, and multi-cloud environments.
This whitepaper illustrates how EmpowerID transforms Entra ID from a Microsoft-centric tool into a comprehensive, versatile solution with:
- Fine-Grained Authorization
- A Vast Integration Network
- Enhanced Risk Analysis
- Access Certification and Recertification
NIS2 Checklist: Preparing for Compliance
Comprehensive NIS2 Compliance Checklist providing a clear roadmap towards meeting the directive's requirements.
Designed for business leaders seeking to fortify their cybersecurity frameworks, the checklist provides actionable insights into the essential components of a successful compliance strategy: the people, the plans, and the partnerships.
Download Checklist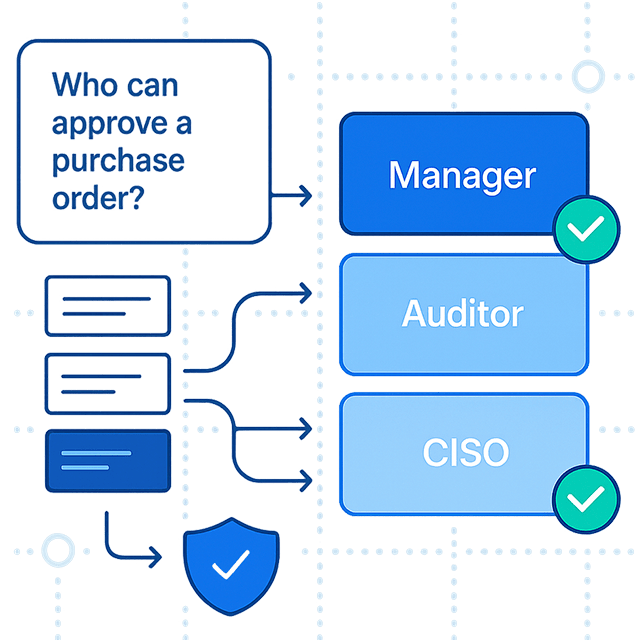
Rethinking the Rush to Policy as Code
Policy as Code (PaC) offers powerful advantages—streamlining policy management, enhancing agility, and integrating seamlessly with DevOps processes. But is your organization rushing in too quickly?
This whitepaper delves into both the benefits and challenges of PaC, providing insights on how to adopt it strategically while maintaining robust security and compliance. Balance agility with security in your IAM strategy.
Download White Paper