Zero Trust Azure Management
Azure & Entra
Cloud IAM Governance
Extend enterprise identity and access management into Azure—govern applications, RBAC, secrets, and OAuth from one control plane built for Zero Trust and least privilege in the cloud.
Business & Technical Benefits
Why CISOs Choose EmpowerID for Azure
Elevate security posture, reduce operational costs, and enable efficient compliance
Business Benefits
- Risk Reduction: Zero Trust and Least Privilege reduce breach risk from insider threats or compromised accounts
- Increased Efficiency: Wizard-style workflows automate complex multi-step Azure processes
- Improved Compliance: Governance capabilities and audit trails facilitate adherence to regulations
- Enhanced UX: User-friendly IAM shopping cart encourages adoption and policy compliance
- Cost Savings: Automation reduces human intervention and operational costs significantly
Technical Benefits
- Enhanced Security: Zero Trust and Least Privilege minimize attack surface and lateral movement
- Visibility & Control: Detailed visibility into each user's access with granular modification control
- Automation & Consistency: Orchestration workflows reduce human error and ensure consistent policy application
- PAM/PIM Support: Pre-approved just-in-time access moves toward zero standing privilege
- Interoperability: Deep Azure integration extends benefits across all applications and services
Built on Zero Trust & Least Privilege
No user or system—inside or outside the perimeter—should be implicitly trusted
Zero Trust Architecture
Application owners perform administrative tasks without native privileged access in Azure—minimizing attack vectors and insider threats.
Least Privilege Administration
Restrict access rights to bare minimum required. Granular control over roles, permissions, secrets, certificates, and OAuth scopes.
Just-in-Time Access
Pre-approved, time-limited access for privileged operations. Zero standing privilege model aligned with PAM/PIM initiatives.
Identity Governance & Analytics
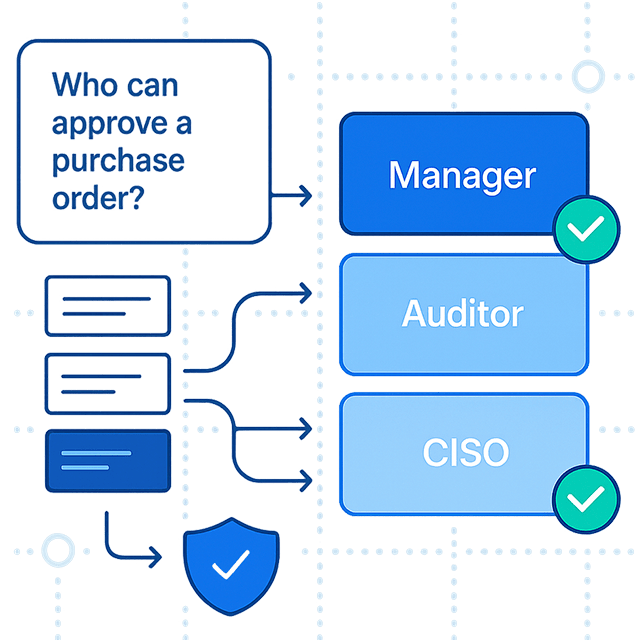
Efficient access request policies, approval workflows, and person-centric inventory. Reliable audit trail for identifying anomalous behavior.
IAM Shopping Cart
User-friendly access request system with flexible approval policies, escalations, and risk analysis. Eligibility policies control visibility.
Wizard-Style Workflows
Intuitive, automated workflows for complex multi-step processes. Reduce human intervention, ensure consistency, cut operational costs.
For Application Owners
As an Application RBAC Owner, I Can...
Complete self-service Azure application management without native privileged access
1 Onboard Applications
Create Azure applications (SAML, SAML Gallery, OIDC) through wizard-style workflows. No native Azure admin access required.
2 Manage Responsible Parties
Assign application owners natively in Azure, plus RBAC Application Owners and Deputies with Zero Trust management rights from EmpowerID only.
3 Control Eligibility
Manage settings controlling who may request access and who is pre-approved in the IAM Shop. Enforce regulatory restrictions and policies.
4 Create Azure App Roles
Create App Roles and automatically create/map Azure AD groups for access requests—reducing direct user account assignments.
5 Vault Secrets & Certificates
View, create, vault, and share client secrets and certificates. Check-in/check-out capabilities for secure application authentication.
6 Manage OAuth Scopes
View and create OAuth Scopes, manage consent settings. Control token configurations including optional claims and claims mapping policies.
7 Manage API Permissions
View and manage both delegated and application API permissions. Ensure secure data access with granular permission control.
8 Person-Centric View
See which users have access to your application and manage assignments. Full visibility into access rights for governance and audit.
9 Location Classification
Assign applications to specific locations for classification. Enable location-based access policies for end users.
Core Capabilities
1 Azure RBAC Management ⌄
- • Comprehensive RBAC management: Manage Azure role assignments, subscriptions, resource groups, and resources.
- • Fine-grained control: Granular security—finally granular security available. Single security model overlays O365 and Azure.
- • Policy-driven assignments: Automated role assignments based on business policies. Continuous enforcement.
- • Continuous reconciliation: Detect drift and reconcile to policy—continuously, not periodically.
- • Audit trails: Full tracking, logging, and reporting. Instant and long overdue pain relief for auditors.
Why it matters: Comprehensive Azure RBAC management. Better than managing separately. Unified governance across Azure services.
2 Entra ID Roles Governance ⌄
- • Self-service Entra ID roles: Application rights and roles governance. Self-service capability for Entra ID roles.
- • Role assignments: Manage Entra ID role assignments automatically. Policy-driven role assignments.
- • Lifecycle management: Automated lifecycle management for Entra ID roles. Onboard, update, and offboard.
- • Compliance: Ensure Entra ID roles comply with business policies. Continuous enforcement.
- • Audit and reporting: Full audit trails for Entra ID role assignments. Easy auditing and recertification.
Why it matters: Entra ID roles governance. Self-service capability. Automated lifecycle management.
3 Azure Application Management (PBAC) ⌄
- • Deep application role management: PBAC stuff—deep application role management. App roles, app rights, detailed Azure application management.
- • Application permissions: Manage Azure application permissions. Fine-grained control over application access.
- • Service principal management: Manage service principals and their permissions. Automated lifecycle management.
- • API permissions: Manage API permissions for Azure applications. Policy-driven permission assignments.
- • Detailed app roles: Manage detailed app roles and app rights. Deep permissions analysis.
Why it matters: Deep application role management (PBAC). This is a huge capability—deep Azure integration.
4 Azure License Management ⌄
- • License optimization: Right-size and reclaim unused entitlements automatically.
- • Automated license assignment: Policy-driven license assignments. Automated lifecycle management.
- • License tracking: Track Azure license usage across all users and services.
- • Cost optimization: Identify unused licenses and reclaim them automatically.
- • Compliance: Ensure license assignments comply with business policies.
Why it matters: License optimization and cost savings. Right-size and reclaim unused entitlements automatically.
5 Unified Azure Governance ⌄
- • All Azure stuff together: RBAC, license management, Entra ID roles, application management—all together in one platform.
- • Single security model: Single security model overlays O365 and Azure. Intercepts and modifies obsolete permissions system.
- • Better than managing separately: Unified governance across Azure services. Better than managing separately.
- • Continuous enforcement: Policy-based enforcement across all Azure services.
- • Complete visibility: Full visibility into all Azure resources, roles, and permissions.
Why it matters: Unified Azure governance—all Azure stuff together. Better than managing separately.
Business Impact
Automated Lifecycle
Eliminate manual provisioning and deprovisioning. Automated lifecycle management for Azure users and resources.
Granular Security
Finally granular security available. Fine-grained control over Azure permissions and roles.
Easy Auditing
Full configurable tracking, logging, and reporting. Instant pain relief for auditors.
FAQs
How is this different from managing Azure separately?
Unified Azure governance—all Azure stuff together (RBAC, license management, Entra ID roles, application management). Better than managing separately. One platform for all Azure governance.
What is PBAC application role management?
Deep application role management (PBAC). App roles, app rights, detailed Azure application management. This is a huge capability—deep Azure integration.
Can we get granular security for Azure?
Yes—finally granular security available. Single security model overlays O365 and Azure. Intercepts and modifies obsolete permissions system. Delivering compliant-level fine-grained security.
How does this help with auditing?
Full configurable tracking, logging, and reporting. Azure's dynamic and expansive system provided major headaches for auditors—this delivers instant and long overdue pain relief.
World's Largest Hybrid Entra ID Transformation
Global Manufacturing Leader
Award Category: IAM at Scale
The Challenge
569,371 person identities across the world's largest hybrid Entra ID/AD landscape with 4.3 million group membership changes per month. Complex hybrid migration from on-premise to Entra ID at massive scale.
EmpowerID Solution
Zero Trust Entra application onboarding and management with real-time processing of millions of monthly changes. Hybrid RBAC/ABAC architecture handling unprecedented transaction volume.